Ransomware or to be specific Crypto Ransomware is the newest trend in malware attacks. A typical Ransomware infection encrypts the victim’s files and holds them hostage unless and until the victim pays a ransom – usually in Bitcoin. The catch here is that, the malware uses industry standard algorithms employing 2048-bit RSA keys coupled with AES encryption routines. With the current computing power at hand, decrypting the data will take lifetimes for a layman. The choice of payment comes down to the question of how badly the victim needs access to the ransomed files, and whether the files lost are worth more than the ransom demand (which is usually only a few hundred dollars in Bitcoin).
The notable Ransomware variants include CTB-Locker, Cryptolocker, Cryptowall, Locky, Teslacrypt, Torrentwall etc. Following is a time-line chart of the notable ransomware discoveries from 2005 to 2016
Added to the above, are more sophisticated variants that turn up frequently. There are way more infections but most of them never see the light of day. We have seen encryption of backups and network storage, entire networks targeted for ransom and not merely opportunistic infection. The targets vary from IT infrastructure to Medical Healthcare.
From educating employees on handling social engineering techniques to backing up data, and from paying ransoms to stockpiling bitcoins, industries are having a hard time fighting against this latest criminal innovation.
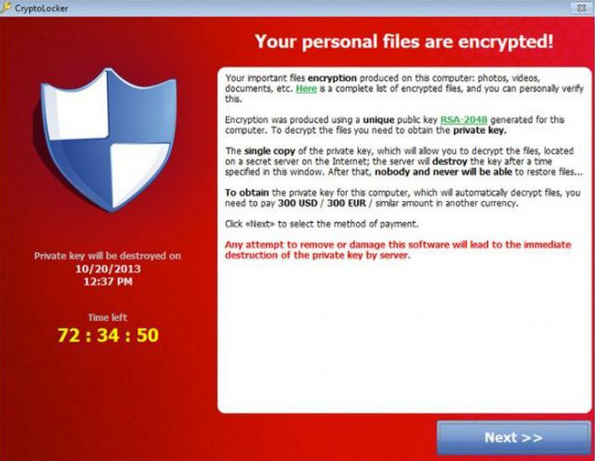
The infamous CryptoLocker Ransomware informing your files are encrypted…forever
The best defense against ransomware is a good set of data backups that are made each day – preferably to a device that is not always connected to the network. Unfortunately, this is often easier said than done.
Companies often employ a variety of steps to prevent ransomware from entering their infrastructure. However, what happens once the malware thwarts all our preventive measures and is within our network? Here we will address how to deploy countermeasures once the ransomware enters our infrastructure. We will be mainly looking at CryptoStalker to address this issue.
CryptoStalker
CryptoStalker is a cross-platform project developed to detect crypto ransomware. It is a port of the original randumb project that was written in python. Both these projects are the work of Sean Williams, a developer from San Francisco. Williams’s father did get infected with an early version of CryptoLocker and hence Williams wanted to create a tool that monitored file systems for newly written files. Coupling this with a way to check if the files contained random data, CryptoStalker was born.
Cryptostalker is simple in terms or its working – detection of entropy in data. It looks for signs of encrypted content, and if they were written at high speed, it would alert the system’s owner.
The difference between CryptoStalker and it’s parent project randumb is the way it checks for new files. randumb uses the linux-specific inotify. While the file notification mechanism used by CryptoStalker is Google’s fsnotify. In this way random/encrypted files will only be detected if they belong to new inodes. This means it will not detetct the following case: a file is opened, truncated, and only then filled in with encrypted content. Fortunately, this is not how most malware works.
Cryptostalker is a work that stands to be refined, but it works as-is to detect common strains of ransomware.
Now let us see how we can perform a minimal setup of CryptoStalker in a Debian environment
Firstly, we need to install Git. Git is a fast, scalable and distributed revision control system designed to handle very large projects with speed and efficiency.
|
# |
Install Go tool for use with gccgo. gccgo is the Go compiler based on gcc backend
|
# |
Download the CryptoStalker sourcecode from GitHub
|
# |
Unzip the cryptostalker-master archive
|
# |
Change to directory cryptostalker-master
|
# |
Source the setup_workspace.sh script. This will download the necessary files, set up a CryptoStalker workspace inside our home directory, and install CryptoStalker into this workspace
|
# |
Now we may start CryptoStalker using any of the following three commands.
This is the default startup option. From now on CryptoStalker will print out a line if even one encrypted file is seen anywhere under directory /tmp
|
# |
For performance reasons, sleep for 100ms after checking each file for randomness
|
# |
This will kill any processes seen starting up 60 seconds before the encrypted file(s) are seen
|
# |
Other notable projects that can be deployed for detecting Ransomware are:
CryptoDrop
CryptoDrop is another much talked about project that was released by a team of researchers from the University of Florida and Villanova University. It was presented on the recently concluded IEEE International Conference on Distributed Computing Systems that took place on June 29 2016 in Nara, Japan.
CryptoDrop is designed to work only on Windows. It keeps an eye on the user’s filesystem for signs and operations specific to ransomware infections. This includes a surge in encryption operations, a drop in available entropy (random data, used to power encryption operations), file type changes (ransomware changes file type extensions), and a few other more.
When CryptoDrop makes a detection of encryption-heavy OS processes, it will stop the process and alert the user that something suspicious is happening. In this way, CryptoDrop will not be able to detect or stop ransomware before encrypting files, but after it already started.
Just like any other generic entropy detector, CryptoDrop has issues with false positives at the process level. CryptoDrop is unable to determine the intent of the changes it inspects. For example, it cannot distinguish whether the user or ransomware is encrypting a set of document. As a result, we can expect programs such as GPG and PGP, compression applications, and other applications which perform similar transformations to cause false positives.
More details can be found in the research paper presented at the IEEE conference, called CryptoLock (and Drop It): Stopping Ransomware Attacks on User Data.
CryptoPrevent
CryptoPrevent is an Anti-Virus/Security Software Supplement, originally designed to prevent infection from the CryptoLocker threat which emerged in late 2013. Since that time, CryptoPrevent has been providing protection against a wide range of ransomware and other malware. A lot of ransomware variants uses the same infection tactics and launch point locations as CryptoLocker. For example there are several copycat strains of this malware — including CryptoWall, CryptoDefense and OnionLocker. Therefore CryptoPrevent is expected to protect against all malware that fits the same or similar profile and behavior. This utility is available from http://foolishit.com/cryptoprevent-malware-prevention
Ransomware Prevention Kit
Once named Cryptolocker Prevention Kit, it was first released in October 2013 to prevent the widespread CryptoLocker infection. The kit includes group policies, filters, settings and instructions including slides and documentation to help secure our Windows OS. The kit is also being updated on a frequent basis. It is available from ThirdTier at http://thirdtier.net/ransomware-prevention-kit. With a small paypal donation of our choice and the sheer amount of information provided, this is a very tempting offer.
SOURCES:
http://resources.infosecinstitute.com
http://news.softpedia.com
http://krebsonsecurity.com
http://github.com/unixist/randumb
http://github.com/unixist/cryptostalker